The Intelligence State and the UFO Problem
Why anomalous evidence is managed before it is explained
The modern UFO story is often told as though seriousness began in 2017. That frame is convenient, but it is not credible. What began in 2017 was not official knowledge of the problem. It was the managed public re-entry of a problem the national security state had already spent decades studying, minimizing, compartmentalizing, and controlling. The subject did not become serious because the New York Times reported on it, because military videos were acknowledged, or because a new vocabulary of UAP replaced the older language of UFOs. Those events changed the public status of the subject. They did not create the underlying record.
That distinction matters. If the public is persuaded that seriousness began in 2017, the state is spared the burden of explaining the preceding seventy years. The old record can be treated as folklore, embarrassment, misperception, or Cold War confusion. The modern process can then be framed as responsible institutions finally looking with fresh eyes at a difficult subject. But the wider evidence points in a different direction. The intelligence state has long understood the UFO problem as a security, technology, custody, and perception-management problem, while allowing the public to treat it as a belief problem.
The prior essay, Disclosure Without Resolution: The UFO Issue as Institutional Containment, examined the current phase: acknowledgment expands, but explanation does not arrive. This essay concerns the deeper structure underneath that pattern. The question is not merely why disclosure remains incomplete. The question is why anomalous evidence is so consistently converted into something else before it can become public truth. Once anomalous evidence enters the intelligence state, it does not remain simply evidence. It becomes a security object, a classification problem, a threat-assessment problem, a technological custody problem, a witness-control problem, and a narrative-risk problem. It is managed before it is explained because the system that receives it is designed for control before truth.
That is the central error in ordinary discussion of the UFO issue. The public is encouraged to debate whether UFOs are real, whether witnesses are credible, whether particular documents are authentic, whether particular officials are telling the truth, or whether particular sightings have conventional explanations. Those questions are not irrelevant, but they are downstream. The upstream question is institutional. What kind of system receives the evidence? What are its incentives? What does it protect? What does it punish? What kinds of truth can pass through it without altering its structure?
The answer is not reassuring. The UFO issue entered institutions built around secrecy, military advantage, technological exploitation, psychological operations, airspace control, nuclear security, contractor dependency, and compartmentalized knowledge. Such institutions do not encounter the unknown as open inquiry. They encounter it as risk. A civilian may see an anomaly and ask what it is. An intelligence system asks what the anomaly exposes, what adversaries might learn from it, what capabilities it implies, what panic it may produce, what sources and methods may be compromised by discussing it, what programs may be revealed, what witnesses must be controlled, and what historical liabilities may arise if the truth is admitted too fully.
Strategic Intent Analysis is useful here because it does not depend on official confession. It asks what systems do repeatedly, selectively, and coherently over time. It does not require proof of a single command structure or a signed order of deception. It looks for directionality, narrative canalization, asymmetric enforcement, institutional lock-in, incentive alignment, and suppression or marginalization of dissent. On that test, the UFO issue produces a strong signal. The state’s behavior has not been random. It has been selective and reinforcing. Serious internal attention coexisted with public ridicule. Technical interest coexisted with official dismissal. Witnesses were discouraged while reports were collected. The subject was stigmatized in public while classified structures preserved access to the underlying evidence.
Australian government files relating to UFOs, made publicly available through the National Archives of Australia by 2011, give this issue particular force. The relevant Department of Defence / Joint Intelligence Bureau material, internally dated 27 May 1971, concerned the “scientific and intelligence aspects of the UFO problem” and included a report on the U.S. attitude compiled from CIA, U.S. Air Force, congressional, and Project Blue Book records. Its importance lies not merely in the fact that Australia held official UFO files, but in how an allied government assessed the American position.
The material describes a divided U.S. posture: public debunking on the surface, deeper intelligence and technical concern underneath. Early U.S. Air Force analysis is described as treating real phenomena as being reported, with performance characteristics beyond known aircraft. The file states that a government agency, inferred to be connected with the CIA Office of Scientific Intelligence, studied UFO reports with an interest in propulsion. It also describes public ridicule not as neutral skepticism, but as a façade serving institutional purposes: reducing public alarm, limiting Soviet exploitation, and covering deeper U.S. work directed toward emulating UFO performance.
That is not the posture of a state encountering nonsense. It is the posture of a state managing danger.
The same material exposes the weakness of the 2017 reset narrative. Long before the modern UAP process, allied defence officials were already distinguishing between the American public story and the American internal story. They understood that Project Blue Book and similar public mechanisms did not exhaust the real intelligence interest. They understood that reports, material, propulsion, weapons effects, and public interpretation were distinct categories. They understood that the question was not simply whether strange things were seen, but whether state systems were quietly studying what those things implied.
This is why official denial cannot be treated as dispositive. A state that has spent decades minimizing and managing the UFO issue cannot be treated as the neutral authenticator of records that would expose the architecture of that management. The ordinary evidentiary reflex is to ask whether the government admits a document is genuine. In this field, that reflex is too naïve. If the document concerns a concealed crash-retrieval or reverse-engineering program, official non-recognition is not unexpected. It is exactly what the structure predicts. The question is not whether the state has blessed the document. The question is whether the document fits the institutional architecture that would necessarily exist if the retrieval allegations are true.
This is the deeper problem examined in Classification and the Limits of Public Accountability. Once evidence is moved inside classified systems, accountability is no longer merely delayed. It is structurally displaced. The public may be told that secrecy is necessary, that sources and methods must be protected, or that national security requires restraint. Sometimes those claims may be partially true. But classification also creates a protected zone in which institutions can hide actions they could not publicly defend. In the UFO context, that means the state’s refusal to authenticate, disclose, or explain cannot be treated as neutral evidence against the underlying reality. It is part of the system being analyzed.
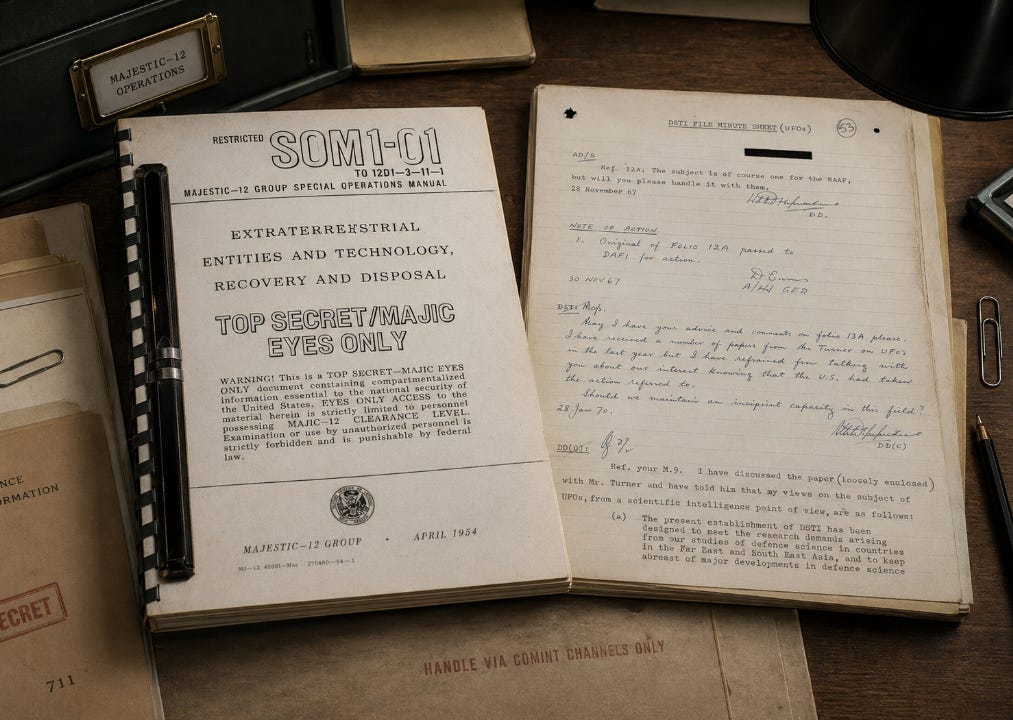
That is where SOM1-01 becomes important. The document purports to be a Majestic-12 Group Special Operations Manual, dated April 1954, titled Extraterrestrial Entities and Technology, Recovery and Disposal. It reportedly surfaced publicly in March 1994, after UFO researcher Don Berliner received an undeveloped roll of 35mm film that, once processed, contained photographs of the manual. Its authenticity has been disputed ever since, largely because it belongs to the contested MJ-12 document family and because critics have alleged anachronisms, formatting issues, and other irregularities. Government-linked responses to MJ-12 material have also denied finding evidence that such material originated in the executive branch.
But the dispute over official authentication does not end the analysis. On this subject, official non-recognition is exactly what the structure would predict if the document were genuine. The significance of SOM1-01 lies in its bureaucratic character. It does not read primarily as myth or speculation. It reads as procedure. It contains chapters and forms dealing with recovery operations, site security, technology recovery, receiving and handling, biological entities, identification, reports, photographs, packaging, transport, isolation, custody, retrieval, preservation, and area cleansing after removal. It describes the operational machinery that would have to exist if crash-retrieval programs existed: securing the site, controlling witnesses, denying or covering the event publicly, tagging and packaging material, transporting it through protected channels, preserving biological remains if present, and removing traces from the recovery area.
A real crash-retrieval program would not operate on rumor. It would produce procedure. It would generate dull language, compartmented access, forms, reporting lines, transport protocols, site-control instructions, and public-containment guidance. It would not be designed to persuade the public. It would be designed to tell cleared personnel what to do when an event occurred. The fact that SOM1-01 reads like a government manual is not incidental. It is the point.
Bureaucratic documents have a recognizable character. They do not usually present themselves dramatically. They allocate responsibility, define categories, reduce uncertainty, preserve control, and tell personnel how to handle exceptional events without improvising. SOM1-01 has that character. It is not genuine because the state admits it. It is probative because it fits what the state would require while also fitting the wider pattern of denial, compartmentalization, technical interest, and witness management.
David Grusch’s testimony changes the context in which such material must be assessed. He did not merely say that there were unexplained objects in the sky. He testified under oath that he had been informed, through official channels, of a multi-decade crash-retrieval and reverse-engineering program. Other testimony has reportedly been provided in classified settings. Eric Davis has also stated that crash retrievals occurred. Whether every detail of every account is established is not the immediate analytical point. The important point is convergence. The claim is no longer only that people saw things. The claim is that state-linked structures possessed things, studied things, concealed things, and denied the existence of the very architecture in which those things were held.
That moves the UFO issue across a decisive threshold. Sightings can be dismissed. Witnesses can be ridiculed. Radar returns can be classified. Videos can be withheld. But recovered material creates a different kind of problem. If a state recovers craft, fragments, components, biological material, or technology that cannot be publicly attributed to a known human source, the issue is no longer merely anomalous observation. It becomes custody. It becomes ownership. It becomes reverse engineering. It becomes contractor access. It becomes weapons potential. It becomes intellectual property. It becomes foreign-acquisition risk. It becomes historical liability.
That is the custody threshold. Before custody, the state can manage reports. After custody, the state must manage objects, programs, contractors, funding, access lists, internal visibility, public denial, and the chain of decisions by which the public was kept outside the truth. The public may still be invited to debate sightings, but the real question has changed. The real question is who possessed the material, who studied it, who funded the work, who was denied oversight, which private entities were involved, what was learned, what was hidden, and how long official institutions maintained a contrary public story while classified structures proceeded on a different factual basis.
This is why the retrieved-craft question cannot be kept separate from the modern disclosure process. A post-2017 story can present UAP as a newly respectable puzzle only if the recovery issue is segregated from the disclosure narrative. Once recovery allegations are integrated, the modern story changes completely. It is no longer a story about serious institutions finally admitting that some reports are unresolved. It is a story about whether serious institutions have been managing the public edge of a classified technological estate for decades.
That possibility explains much of the institutional behavior that otherwise appears incoherent. It explains why the subject could be ridiculed while still being collected. It explains why witnesses could be degraded while classified interest continued. It explains why public investigations could be underpowered while sensitive channels remained protected. It explains why government statements can acknowledge anomalies while refusing historical resolution. It explains why language shifts from UFO to UAP, why disclosure moves procedurally but not substantively, and why the system repeatedly concedes enough to preserve credibility while withholding enough to preserve custody.
It also explains why the public record feels fractured. Fracture is not necessarily a failure of the system. It may be the system. Mature secrecy structures do not merely hide information from outsiders. They prevent full internal visibility. They distribute knowledge across compartments, contracts, clearances, locations, and legal fictions so that very few people can see the whole. As discussed in Compartmentalization and the Structure of Classified Power, the point of such structures is not simply to keep secrets from the public. It is to make the secret difficult to assemble even inside the state. A retrieval program hidden inside that architecture would not look like one clean file. It would look like fragments: budget traces, contractor programs, witness accounts, classified briefings, anomalous materials language, legacy access disputes, and documents the state refuses to recognize.
The military-industrial structure intensifies the problem. If recovered technology exists, the state would almost certainly move it into environments capable of protecting and exploiting it: defence contractors, special access programs, restricted laboratories, military research channels, and intelligence-linked technical compartments. As discussed in The Military-Industrial Complex and the Persistence of Secrecy, exposure does not automatically dissolve such structures. It can be absorbed. A system can acknowledge a public controversy while preserving the classified programmatic core beneath it. That is why disclosure can expand without resolution. The visible layer moves; the custody layer remains protected.
The role of ridicule should also be understood structurally. Ridicule was not merely cultural noise. It was a low-cost method of boundary enforcement. It discouraged pilots, service members, scientists, journalists, and officials from treating the subject as professionally safe. It made reporting reputationally expensive. It allowed serious material to be buried inside an environment of absurdity. It separated internal collection from public legitimacy. In SIA terms, it functioned as narrative canalization and asymmetric enforcement. The state could collect reports while the witness paid the social cost of reporting them. The institution preserved access to the evidence while reducing the number of people willing to make the evidence matter publicly.
That is why the modern turn toward controlled seriousness should not be mistaken for transparency. It is better understood as adaptation. The old ridicule model became less sustainable once military videos, congressional attention, whistleblower claims, and public distrust reached a certain threshold. The system did not collapse. It changed form. The subject was reintroduced under safer language, safer channels, safer procedures, and a safer starting point. Seriousness was restored, but memory was narrowed. The public was allowed to know that the issue exists, but not to fully revisit what the state previously knew, did, denied, recovered, studied, or concealed.
This is disclosure without memory. It allows the present to appear responsible while the past remains unaccounted for. It says, in effect: serious people are now looking at this. It does not answer why serious people were looking at it in 1947, 1952, 1953, 1966, 1969, or throughout the hidden years that followed. It does not explain why allied defence officials described a public-private split decades ago. It does not explain why official structures contemplated material handling. It does not explain why witnesses were discredited while data was collected. It does not explain why crash-retrieval allegations now converge across testimony, documents, historical patterns, and bureaucratic necessity.
The most important fact may therefore be not any single sighting, witness, manual, memo, or official statement. It may be the pattern of convergence. The Australian file describes the public façade and the internal technical concern. SOM1-01 describes the operational architecture that would be needed if retrieval occurred. Grusch and Davis point toward a legacy crash-retrieval and reverse-engineering structure. The broader state record shows stigma, classification, compartmentalization, contractor dependency, and managed public acknowledgment. These are not isolated curiosities. They point toward the same institutional form.
The intelligence state has not behaved like a system trying to explain an anomaly to the public. It has behaved like a system trying to retain control over an anomaly’s consequences. That is a different thing. Explanation would require opening the evidence, integrating the history, reconciling public denial with internal knowledge, and accounting for the custody question. Management requires only that the subject remain procedurally contained. It can be acknowledged without being resolved. It can be studied without being opened. It can be serious without being accountable.
That is why the UFO problem remains structurally unresolved. The issue is not simply that the public lacks information. It is that the evidence has been routed through institutions whose primary function is to preserve advantage, not produce shared reality. The state does not ask first what the public has a right to know. It asks what the evidence might expose, what it might destabilize, what it might reveal about hidden programs, and what consequences would follow if the old public story had to be abandoned.
The modern disclosure process therefore cannot be understood as a clean movement from ignorance to inquiry. It is better understood as the controlled public reappearance of a long-managed problem. The public is told that the government is now taking anomalies seriously. But the deeper record suggests that the state took them seriously long ago, and that the real issue has always been how much seriousness could be safely admitted.
If crash retrievals occurred, then the central question was never merely whether objects were seen. It was whether objects were held. The public was invited to debate sightings while the deeper issue was custody. That is the point at which the UFO problem becomes inseparable from the intelligence state. A recovered craft is not only evidence. It is a strategic asset, a classified object, a technological prize, a liability, and a threat to the official history of the last seventy years.
The intelligence state can survive sightings. It can survive anomalies. It can survive partial disclosure. What it cannot easily survive is an integrated account of custody: who had the material, who studied it, who benefited from it, who lied about it, who was denied oversight, and how much of modern technological and military history sits in the shadow of that concealment. That is why anomalous evidence is managed before it is explained. Explanation would lead backward into memory, inward into custody, and outward into accountability. Management keeps all three contained.
The problem, then, is not that the state has failed to answer the UFO question. The problem is that the state has repeatedly converted the UFO question into a state-security problem before the public was allowed to ask it properly. The anomaly disappears behind classification. The witness disappears behind stigma. The document disappears behind non-recognition. The object, if recovered, disappears behind custody. And the history disappears behind a modern story that pretends seriousness began only when the system decided it was safe to admit seriousness.
That is no longer credible. The evidence does not require institutional permission to become analyzable. The state’s refusal to authenticate its own hidden architecture is not a veto over reality. Under Strategic Intent Analysis (SIA), the pattern is the evidence: public denial paired with internal concern, ridicule paired with collection, disclosure paired with non-resolution, and retrieval allegations paired with precisely the kind of bureaucratic machinery retrieval would require. The intelligence state does not merely conceal the UFO problem. It changes the form in which the problem is permitted to exist.
That is why the issue persists. It is not only a mystery in the sky. It is a mystery inside power. Until the custody question is answered, every public disclosure will remain partial, every denial will remain structurally suspect, and every explanation will arrive already shaped by the system that had the strongest reason to manage the evidence before the public could understand what it meant.