Classification and the Limits of Public Accountability
Why states can hide actions they could not publicly defend
Secrecy can have legitimate uses. States sometimes need to protect sources, methods, negotiations, and operations whose exposure would cause real harm. But that ordinary justification does not resolve the harder constitutional question. Once conduct is placed behind a classified wall, the normal tests by which a free society distinguishes lawful protection from unlawful abuse become weaker, slower, and sometimes nearly unavailable. Public criticism cannot attach to what cannot be seen. Courts often defer where they cannot examine the underlying material openly. Legislatures are briefed selectively, late, or in constrained form. Journalism can suspect but not verify. Citizens are told to trust not because the conduct has been shown to be lawful, but because the state says the subject itself cannot be publicly judged.
That is why classification is not merely a storage system for sensitive information. It can also function as immunity from public accountability. The relevant question is not whether every classified program is unlawful. The relevant question is whether classification can preserve conduct that would have faced severe legal, political, and moral challenge if exposed in real time. The documented record shows that it can. More than that, it shows something deeper: institutions created in the name of protection can become instruments of violation, while secrecy delays scrutiny until the moment of practical restraint has already passed.
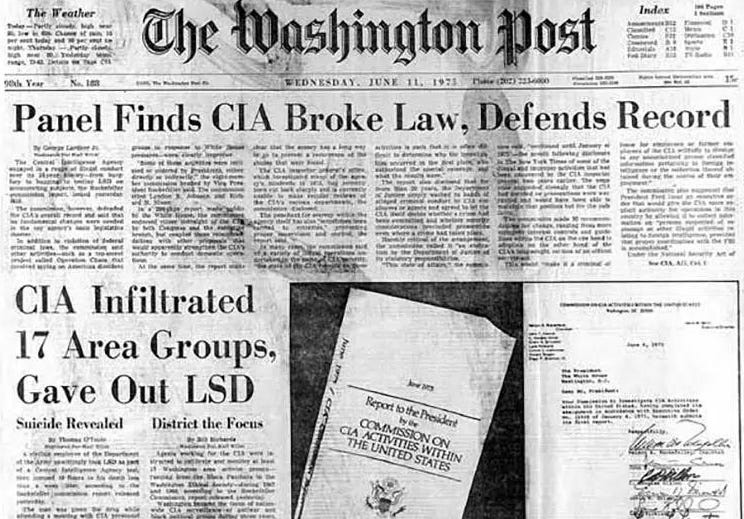
The domestic examples are especially revealing because they show protective institutions turning inward against the people they were supposedly meant to serve. The Church Committee record and later CIA historical review make clear that programs such as MHCHAOS and COINTELPRO were not ordinary foreign intelligence work. They involved covert monitoring, disruption, and repression directed at Americans engaged in political activity protected by the Constitution. Americans were watched, files were built, groups were infiltrated, and protected speech was treated as a security problem. That was not protection. It was covert state action against the rights of the people the state claimed to defend.
MKULTRA shows the same inversion in even starker form. It was not merely reckless drug experimentation. It was a covert CIA program of research into behavioral modification, mind control, interrogation, and the control of human behavior. Human beings, including unwitting subjects, were used in secret experiments involving LSD and other techniques designed to break down autonomy and develop methods of manipulation. The point was not medical treatment or public safety. The point was domination. Classification did not merely hide embarrassing excess. It concealed a secret state effort to develop techniques of control through human experimentation that would have been impossible to defend under ordinary legal, ethical, or democratic scrutiny.
The surveillance record points in the same direction. ECHELON existed. It was a system of large-scale interception of private and commercial communications. A capability of that kind is not meaningfully compatible with the Bill of Rights. It is the opposite of particularized, warrant-bound, publicly challengeable government intrusion. The more important question is what happened after exposure. The answer is not abandonment. The answer is continuity through adaptation. The later surveillance record shows the same operating logic reappearing through new technical systems, new legal rationales, and deeper layers of classification. Bulk collection, mass interception, retrospective access, and normalized secrecy did not vanish. They evolved. The system did not retreat from these capabilities. It preserved them.
That is why the later disclosures matter. They did not reveal isolated overreach at the margins. They revealed a surveillance architecture of immense constitutional consequence operating far beyond ordinary public judgment. The public learned, long after the capabilities were functioning, that intelligence services had built systems of monitoring and access incompatible with the idea of a free citizenry secure from generalized hidden search. During the Boston Marathon investigation, former FBI agent Tim Clemente casually stated on television that on the national-security side authorities could go back and review communications. That remark mattered not because one television interview settled every technical question, but because it reflected a broader reality already visible in the record: insiders spoke as if retrospective communications access was normal because mass surveillance capability had become normal inside the classified system.
The foreign record widens the same logic. Classified covert action has repeatedly concealed intervention, destabilization, regime change, manipulation, and political violence abroad. The overthrow of Prime Minister Mossadegh in Iran and the regime support structure around Pinochet in Chile are not side notes to the story. They are central illustrations of how states speak in the language of law, sovereignty, democracy, and security while acting in ways that violate those same principles when power judges the result worth the cost. Classification did not create the will to do these things. It protected the gap between public principle and operational reality. It allowed governments to deny in public what they were directing in secret.
This is the deeper lesson of the record. The problem is not only that hidden abuses occur. It is that classification changes the burden of justification. In open government, power ordinarily acts under at least some risk of contemporaneous challenge. Policies may still be wrong, abusive, or unconstitutional, but they must usually survive visible argument, adversarial testing, and the possibility of immediate restraint. In classified environments that sequence inverts. Action comes first. Scrutiny comes later, if it comes at all. Exposure arrives after the objective has already been pursued. Reports are written. Hearings are held. Reforms are promised. The system protects itself and continues.
Truth That Changes Nothing is the most direct companion essay because the problem is not only concealment, but what happens when concealment fails. That essay argues that institutions can absorb disruptive truths without permitting those truths to alter the underlying structure of power. The same pattern applies here. Classified misconduct may eventually become visible, hearings may be held, reports may be written, and public outrage may briefly surface, yet the underlying machinery often survives with little proportional correction. In that sense, classification does not merely hide abuse while it is occurring. It helps convert later exposure into a managed aftermath rather than an effective limit on future conduct.
Operation Northwoods: A Completed Conspiracy, Not a Theory deepens the argument by focusing on what Northwoods actually demonstrates. Northwoods was a documented Joint Chiefs plan to stage attacks, killings, and terror against Americans or on U.S. soil, blame them on Cuba, and use the resulting outrage to justify war. Its relevance here is exact. Classification does not merely hide acts already carried out. It can also conceal executable planning for acts that would have been politically monstrous, legally indefensible, and morally unforgivable if exposed while still live. Northwoods therefore shows that the classification system shields not only misconduct, but prepared institutional willingness for extreme misconduct.
Epstein the System: An Institutional Analysis extends this essay beyond formal classification into the broader structure of protected misconduct. That essay shows that Epstein was not an aberration but a systemic function: a figure contained, processed, and ultimately neutralized by the very institutions charged with preventing what he did. Its central point is that the American system did not fail through ignorance or evidentiary weakness. It contained through procedure. The 2008 non-prosecution agreement, the secret narrowing of exposure, the conversion of later revelations into spectacle without proportionate consequence, and the sacrifice of peripheral figures while the wider structure remained intact all reveal the same logic. The connection here is direct. What classification does by secrecy in one register, institutional containment can do by procedure in another. In both cases, the function is the same: protect the structure, narrow the field of consequence, and ensure that truth does not travel upward into real accountability.
That pattern becomes even clearer when placed beside Epstein’s elite and intelligence-adjacent proximity. Epstein’s world overlapped with state-linked and intelligence-adjacent circles, and later reporting showed contact with figures at the highest levels of power, including William Burns before Burns became CIA director. That proximity matters because it shows how deeply compromising conduct can remain embedded near the highest levels of institutional life without producing decisive rupture. It is evidence of a protection environment in which fragmentation of knowledge, elite access, and non-consequence matter more than formal denial. What formal classification accomplishes directly in secret programs, elite insulation can accomplish indirectly through protected networks, selective inaction, and the management of consequence.
Nord Stream and the Discipline of Reality carries the argument into the geopolitical present by examining what the destruction of the pipelines actually revealed. That essay shows that Nord Stream was a deliberate act of infrastructure warfare that permanently removed a strategic option Europe might otherwise have used to limit escalation, restore cheap energy, or recover bargaining flexibility. More revealing than the explosion itself was the system response that followed: no serious restoration effort, rapid energy reordering, and behavior that treated the loss as final from the start. Applying Strategic Intent Analysis, U.S. responsibility is the analytically obvious explanation of the event. Its relevance here is direct. Classification does not only hide completed operations. It also helps preserve the public illegibility of acts whose strategic meaning is perfectly clear in outcome. Reality is changed, the beneficiaries are visible, the system locks in the result, and public accountability remains blocked.
The citizen is told that secrecy is necessary for protection. Yet the record repeatedly shows secrecy being used to conceal actions taken against the rights, interests, and sovereignty of those supposedly being protected, both at home and abroad. That is not a minor abuse at the edge of an otherwise healthy system. It is an inversion risk built into any structure that permits institutions to decide in secret both what they may do and what the public may know about what they have done.
A constitutional order depends not only on rights in theory, but on the practical possibility of knowing when they are being crossed. Where classification prevents that knowledge, it does more than hide information. It suspends judgment itself. And once judgment is suspended long enough, accountability becomes retrospective theater rather than an operating limit on power.